We can't find the internet
Attempting to reconnect
Something went wrong!
Attempting to reconnect
Mercando was designed from the ground up with enterprise-grade security at every layer. Every document, every action, every access is protected by a comprehensive security architecture that meets the strictest compliance requirements.
Layered protection for company data. Every document passes through five independent security layers, ensuring protection at rest, in transit, and during every interaction.
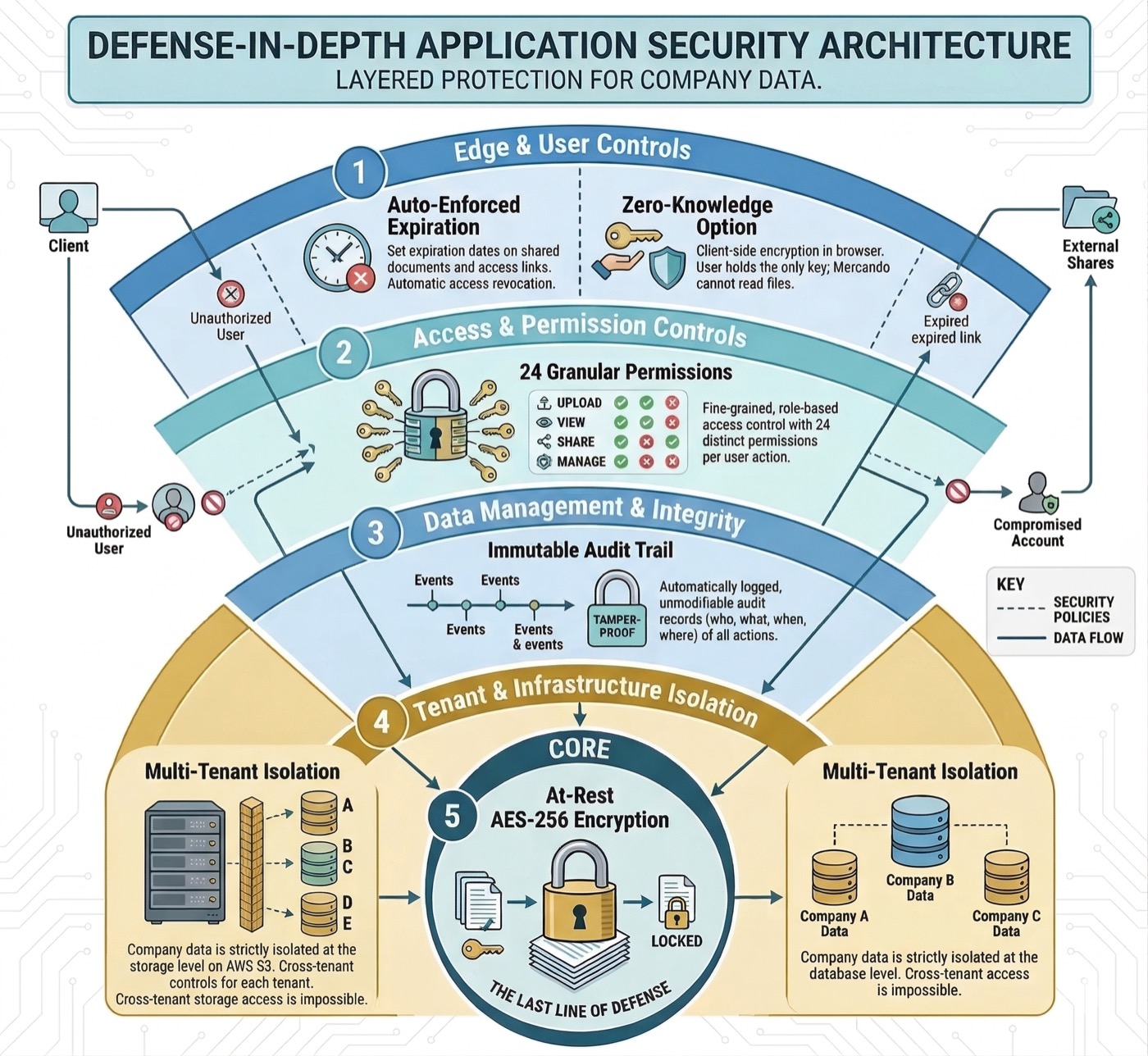
Auto-enforced expiration revokes access when time is up. Zero-knowledge encryption ensures documents are encrypted in your browser before upload -- not even Mercando can read your files.
Fine-grained, role-based access control with 24 distinct permissions per user action. Define exactly who can upload, view, share, or manage documents.
Immutable audit trail with automatically logged, tamper-proof records of all actions -- who, what, when, and where. Audit logs cannot be modified or deleted, even by administrators.
Every company's data is strictly isolated at the database level. Cross-tenant access is architecturally impossible. Each query is scoped to the authenticated company.
The last line of defense. Every document is encrypted at rest using AES-256, the same standard used by governments and financial institutions. Encryption keys are managed per-version.
Multiple authentication methods and strict access controls ensure only authorized users reach your documents.
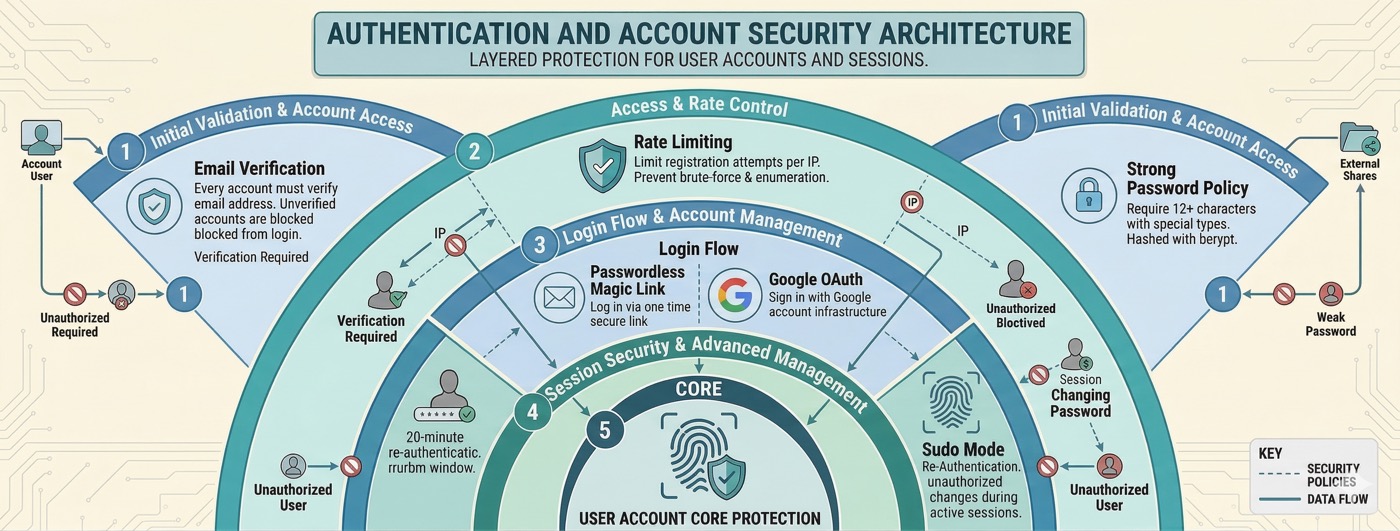
Passwords require a minimum of 12 characters with uppercase, lowercase, and digit or special character. Hashed with bcrypt for storage.
Log in without a password using a secure, one-time email link. Proves email ownership on every login, similar to two-factor authentication.
Sign in with your Google account for streamlined access. Leverages Google's own security infrastructure, including their two-factor authentication.
Every account must verify their email address before gaining access. Unverified accounts are blocked from logging in.
Sensitive operations like changing your password or email require re-authentication within a 20-minute window, preventing unauthorized changes even with an active session.
Automated abuse protection limits registration attempts per IP address, preventing brute-force attacks and account enumeration.
Enterprise-grade infrastructure with defense-in-depth protections at every layer of the stack.
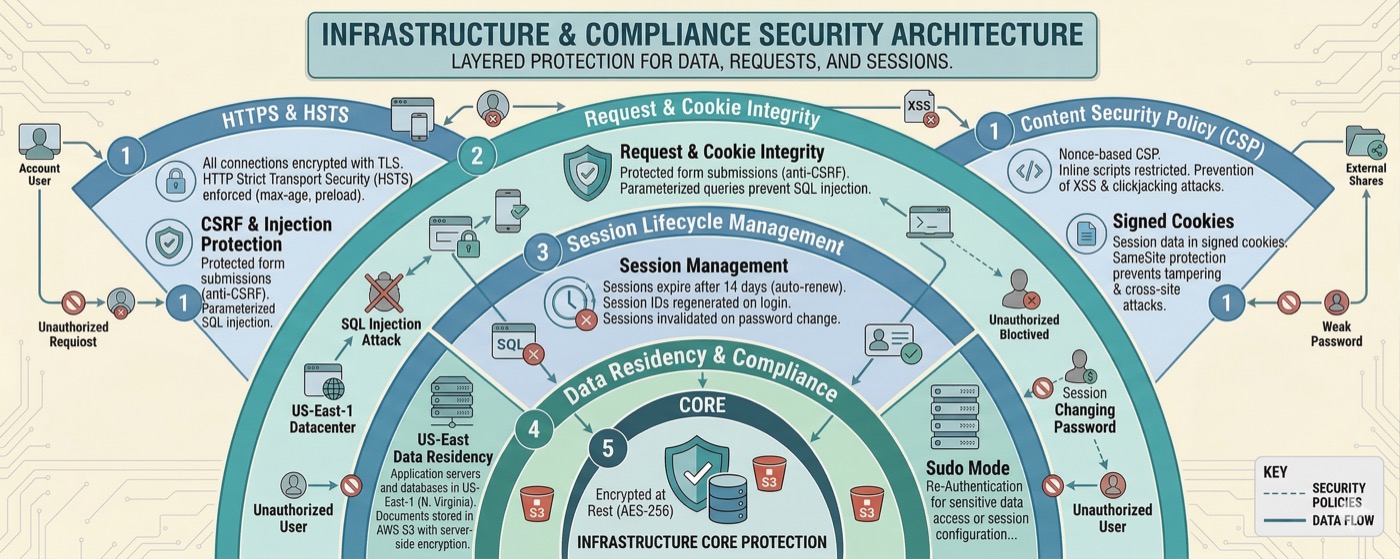
All connections are encrypted with TLS. HTTP Strict Transport Security is enforced with a one-year max-age, preload, and subdomains included.
Nonce-based Content Security Policy prevents cross-site scripting (XSS) and clickjacking attacks. Inline scripts are restricted to cryptographically verified sources.
Application servers and databases are hosted in US-East-1 (Northern Virginia). Documents are stored in AWS S3 with server-side encryption in the same region.
Sessions expire after 14 days with automatic renewal. Session IDs are regenerated on login to prevent fixation attacks. All sessions are invalidated on password change.
All form submissions are protected against cross-site request forgery. Parameterized queries prevent SQL injection. OAuth flows use state parameters to prevent CSRF.
Session data is stored in cryptographically signed cookies with SameSite protection, preventing tampering and cross-site attacks.
If you discover a security vulnerability, we encourage responsible disclosure. Please report any security concerns to our dedicated security team.
security@nimbbo.comWe acknowledge all reports within 48 hours and work to resolve confirmed vulnerabilities promptly.
Mercando's architecture is designed to meet and exceed the most demanding regulatory frameworks in financial services and data protection.
Our controls are designed to meet SOC 2 Type II requirements across security, availability, and confidentiality trust service criteria.
Full compliance with the General Data Protection Regulation, including data minimization, consent management, right to erasure, and data processing agreements.
Our information security management system aligns with ISO 27001 controls, providing a systematic approach to managing sensitive company information.
Built with the technical safeguards required by HIPAA, including encryption, access controls, audit logging, and automatic session management for healthcare data.
With Zero-Knowledge encryption enabled, your documents are encrypted directly in your browser using AES-256 before they ever leave your device. The encryption key never touches our servers.
Encryption happens in your browser using the Web Crypto API. Your plaintext data never leaves your device.
The encryption key is generated and stored locally. Without it, the encrypted file is unreadable -- even to Mercando staff and infrastructure.
When you or an authorized recipient downloads the file, decryption happens automatically in the browser. The experience is transparent and effortless.
Select Document
Choose file and enable client-side encryption
Browser Encrypts
AES-256 encryption happens locally in your browser
Encrypted Upload
Only encrypted data reaches Mercando servers
Secure Storage
Stored encrypted -- unreadable without your key
Join companies that trust Mercando to protect their most sensitive compliance documents. Start for free with full security features included.
Sign Up Free